This post is one of a series of packet capture analysis challenges designed to test your ability to understand what is going on in a network from packet captures.
Download the Packet Capture and see how many of the questions you can answer from the attached packet capture.
The answers are at the bottom of this page, along with how we got to the answers.
This challenge focuses on the Evolved Packet Core, specifically the S1 and Diameter interfaces.
Why is the Subscriber failing to attach?
And what is the behavior we should be expecting to see?
What is the Cell ID of this eNodeB?
What is the Tracking Area?
That the subscriber is trying to attach in.
Does the device attaching to the network support VoLTE?
What type of IP is the subscriber requesting for this PDN session?
Is the device requesting an IPv4 address, IPv6 address or both?
What is the Diameter Application ID for S6a?
You should be able to ascertain this from information from the PCAP, without needing to refer to the standards.
What is the Crytpo RES returned by the HSS, and what is the RES returned by the SIM/UE?
Does this mean the subscriber was authenticated successfully?
Answers
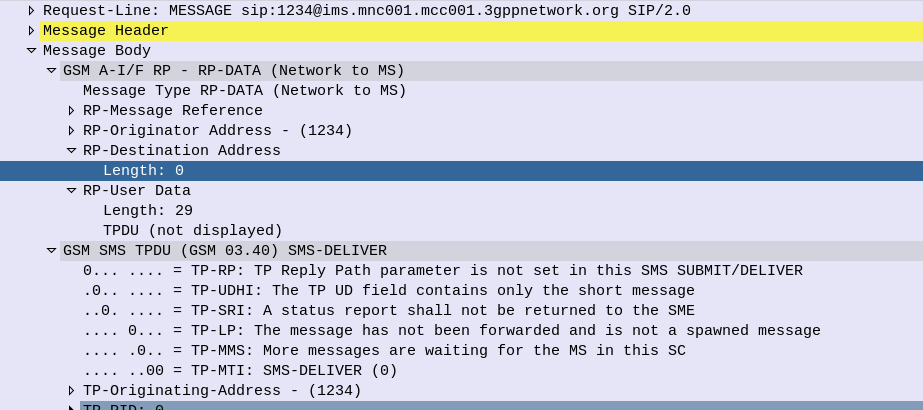
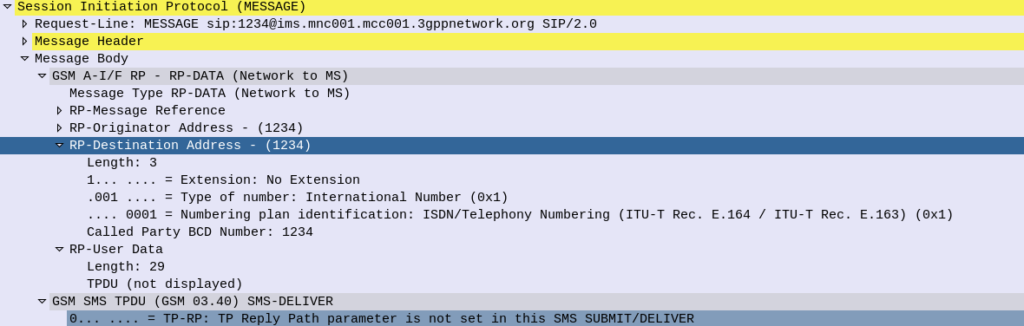
Answer: Why is the Subscriber failing to attach?
The Diameter Update Location Request in frame 10 does not get answered by the HSS. After 5 seconds the MME gives up and rejects the connection.
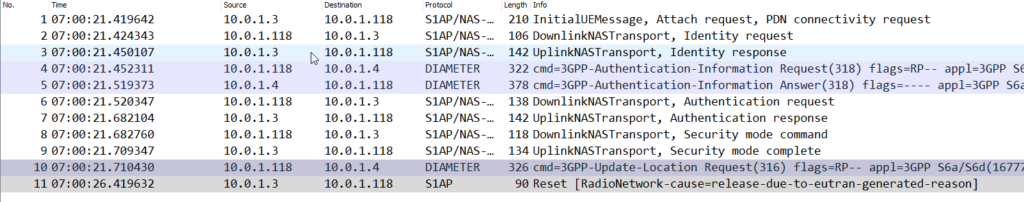
Instead what should have happened is the HSS should have responded to the Update Location Request with an Update Location Answer, as we covered in the attach procedure.
Answer: What is the Cell ID of this eNodeB?
In Uplink messages from the eNodeB the EUTRAN-GCI field contains the Cell-ID of the eNodeB.
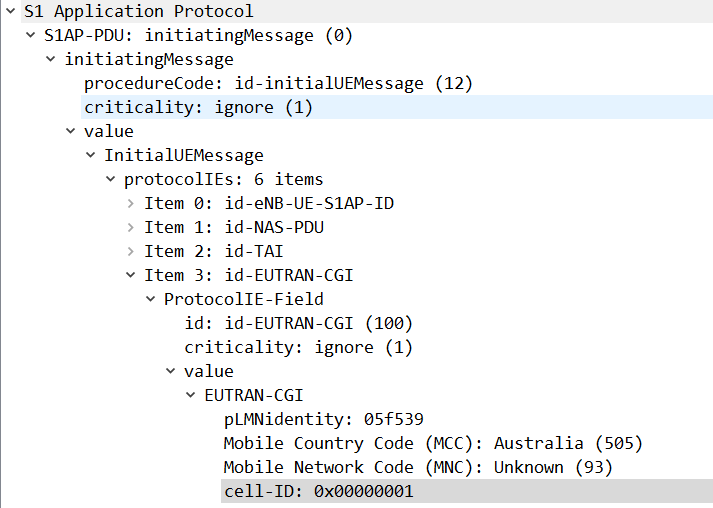
In this case the Cell-ID is 1.
Answer: What is the Tracking Area?
The tracking area is 123.
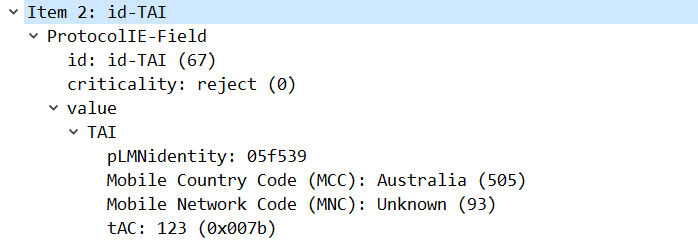
This information is available in the TAI field in the Uplink S1 messages.
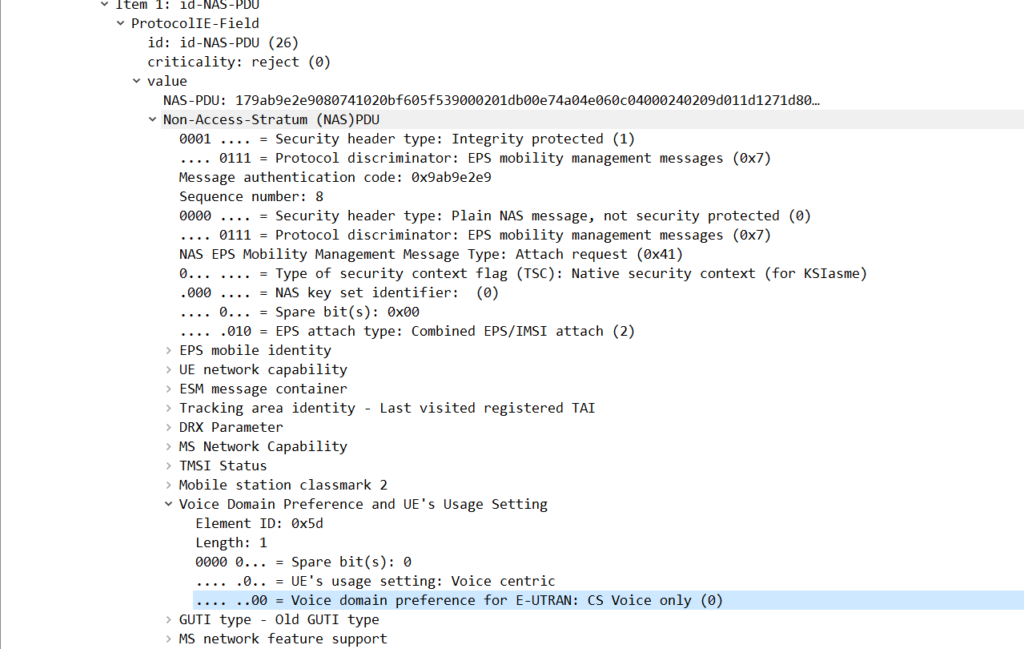
Answer: Does the device attaching to the network support VoLTE?
No, the device does not support VoLTE.
There are a few ways we can get to this answer, and VoLTE support in the phone does not mean VoLTE will be enabled, but we can see the Voice Domain preference is set to CS Voice Only, meaning GSM/UMTS for voice calling.
This is common on cheaper handsets that do not support VoLTE.
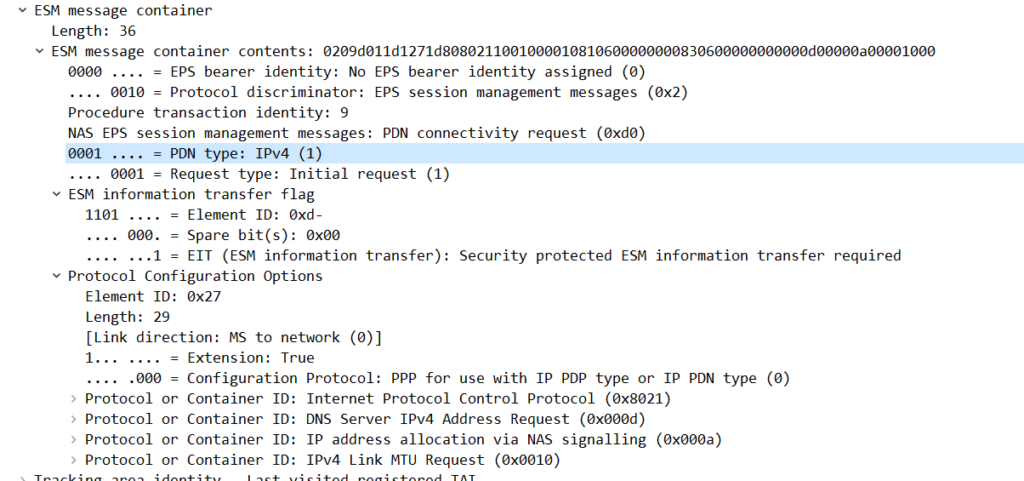
Answer: What type of IP is the subscriber requesting for this PDN session? (IPv4/IPv6/Both)?
The subscriber is requesting an IPv4 address only.
We can see this in the ESM Message Container for the PDN Connectivity Request, the PDN type is “IPv4”.
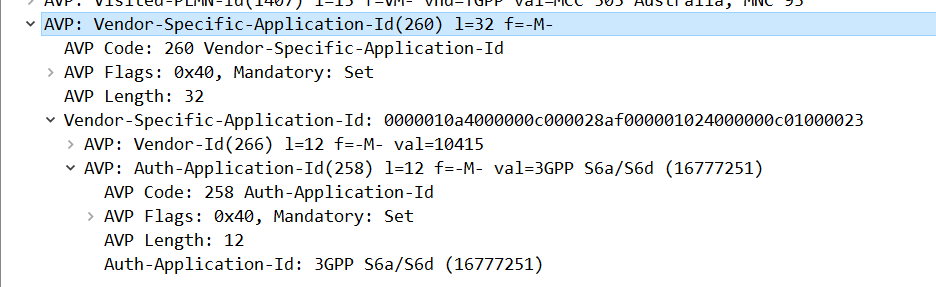
Answer: What is the Diameter Application ID for S6a?
Answer: 16777251
This is shown for the Vendor-Specific-Application-Id AVP on an S6a message.
Answer: What is the Crytpo RES returned by the HSS, and what is the RES returned by the SIM/UE?
The RES (Response) and X-RES (Expected Response) Both are “dba298fe58effb09“, they do match, which means this subscriber was authenticated successfully.