Okay, so a little late to the party on this one…
The other day I had to setup a TDM (E1) based SS7 link (oh yes my friend – they still exist) to interconnect with another operator.
I’m using Cisco’s ITP product as the STP / Signaling Gateway, and my trusty port mirror for what’s going on doesn’t extend down to TDM links.
But I found out you can mirror MTP3 traffic from TDM links in the STP!
Firstly we’ve got to define the remote destination to send the TDM mirrored traffic to, and an access list to match all SS7 traffic:
cs7 paklog your.ip.for.sniffing dest-port 514
access-list 2700 instance 0 permit all
Next up we start a debug session for traffic matching that access list:
debug cs7 mtp3 paklog 2700
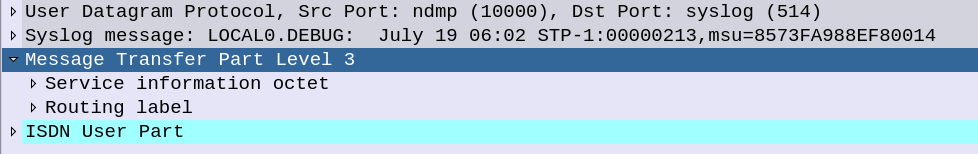
And then over on your monitoring box (the IP you specified in your.ip.for.sniffing ) fire up Wireshark and voila!
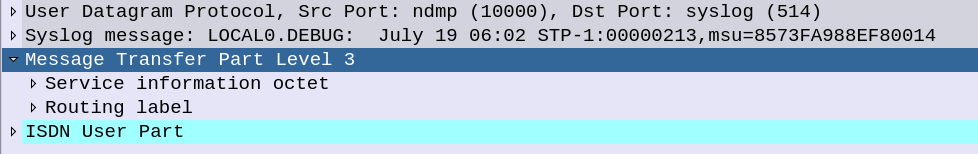
All our MTP3 traffic!
This was super useful for ensuring the ITP was working correctly as a signaling gateway and passing the M3UA packets over onto MTP3 MSUs.