There’s a lot of layers of signalling in the LTE / EUTRAN attach procedure, but let’s take a look at the UE attach procedure from the Network Perspective.
We won’t touch on the air interface / Uu side of things, just the EPC side of the signaling.
To make life a bit easier I’ve put different signalling messages in different coloured headings:
Blue is S1AP
Orange is Diameter
Green is GTP-C (GTP-v2)
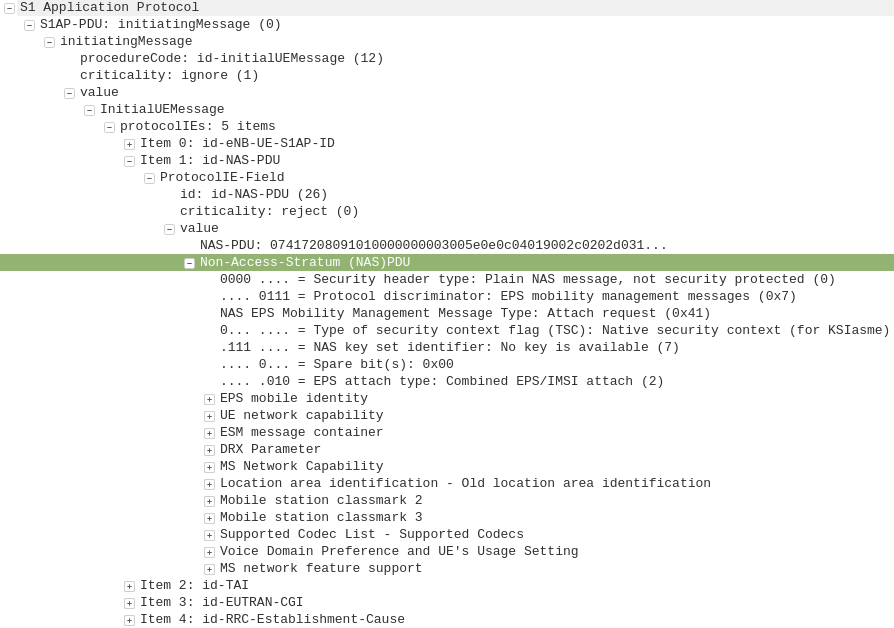
S1AP: initiating Message, Attach Request, PDN Connectivity Request
eNB to MME
After a UE establishes a connection with a cell, the first step involved in the attach process is for the UE / subscriber to identify themselves and the network to authenticate them.
The TAI, EUTRAN-CGI and GUMME-ID sections all contain information about the serving network, such the tracking area code, cell global identifier and global MME ID to make up the GUTI.
The NAS part of this request contains key information about our UE and it’s capabilities, most importantly it includes the IMSI or TMSI of the subscriber, but also includes important information such as SRVCC support, different bands and RAN technologies it supports, codecs, but most importantly, the identity of the subscriber.
If this is a new subscriber to the network, the IMSI is sent as the subscriber identity, however wherever possible sending the IMSI is avoided, so if the subscriber has connected to the network recently, the M-TMSI is used instead of the IMSI, and the MME has a record of which M-TMSI to IMSI mapping it’s allocated.
Diameter: Authentication Information Request
MME to HSS
The MME does not have a subscriber database or information on the Crypto side of things, instead this functionality is offloaded to the HSS.
I’ve gone on and on about LTE UE/Subscriber authentication, so I won’t go into the details as to how this mechanism works, but the MME will send a Authentication-Information Request via Diameter to the HSS with the Username set to the Subscriber’s IMSI.
Diameter: Authentication Information Response
HSS to MME
Assuming the subscriber exists in the HSS, a Authentication-Information Answer will be sent back from the HSS via Diameter to the MME, containing the authentication vectors to send to the UE / subscriber.
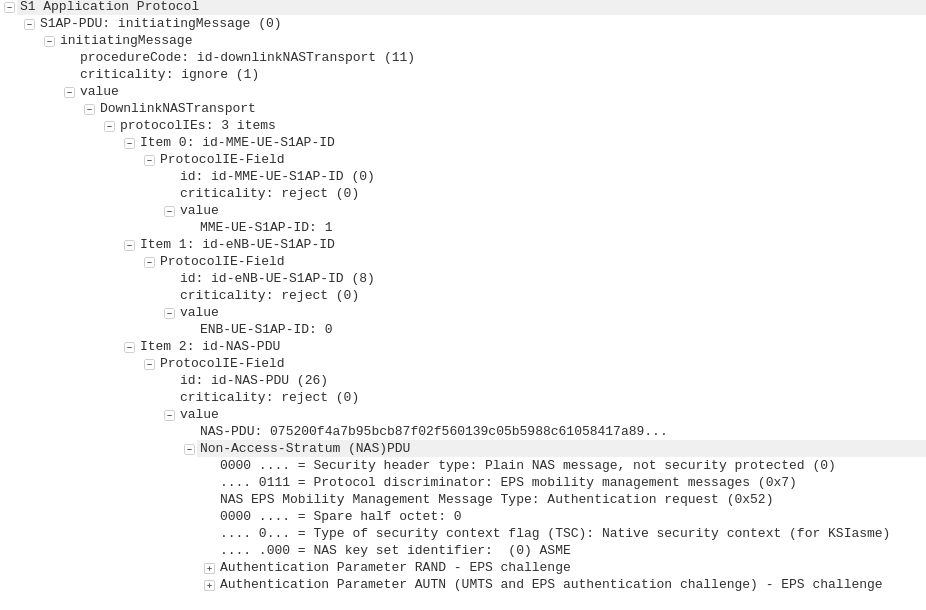
S1AP: DownlinkNASTransport, Authentication request
MME to eNB
Now the MME has the Authentication vectors for that UE / Subscriber it sends back a DownlinkNASTransport, Authentication response, with the NAS section populated with the RAND and AUTN values generated by the HSS in the Authentication-Information Answer.
The Subscriber / UE’s USIM looks at the AUTN value and RAND to authenticate the network, and then calculates it’s response (RES) from the RAND value to provide a RES to send back to the network.
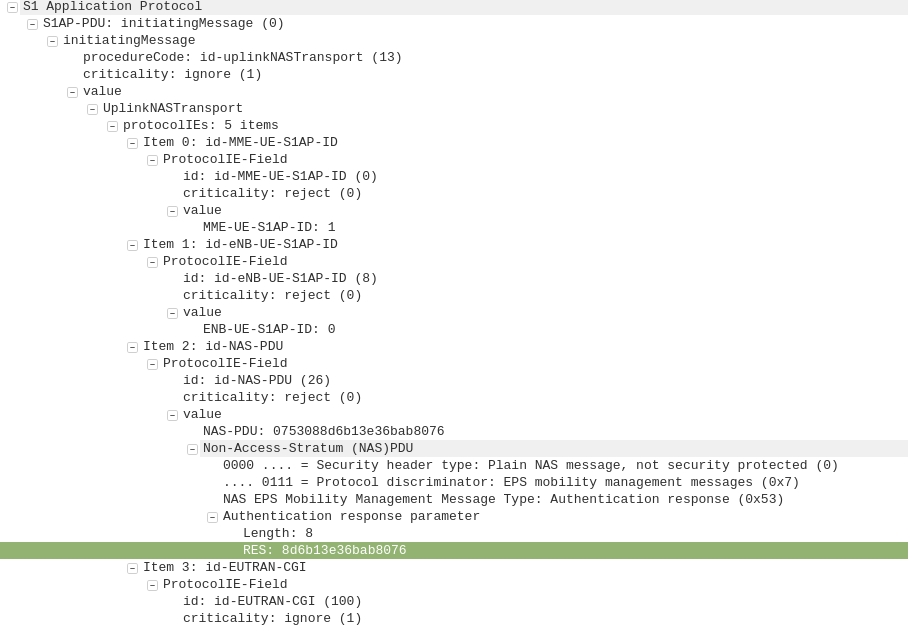
S1AP: UplinkNASTransport, Authentication response
eNB to MME
The subscriber authenticates the network based on the sent values, and if the USIM is happy that the network identity has been verified, it generates a RES (response) value which is sent in the UplinkNASTransport, Authentication response.
The MME compares the RES sent Subscriber / UE’s USIM against the one sent by the MME in the Authentication-Information Answer (the XRES – Expected RES).
If the two match then the subscriber is authenticated.
I have written more about this procedure here.
S1AP: DownlinkNASTransport, Security mode command
MME to eNB
The DownlinkNASTransport, Security mode command is then sent by the MME to the UE to activate the ciphering and integrity protection required by the network, as set in the NAS Security Algorithms section;
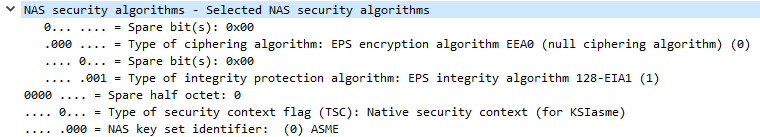
The MME and the UE/Subscriber are able to derive the Ciphering Key (CK) and Integrity Key (IK) from the sent crypto variables earlier, and now both know them.
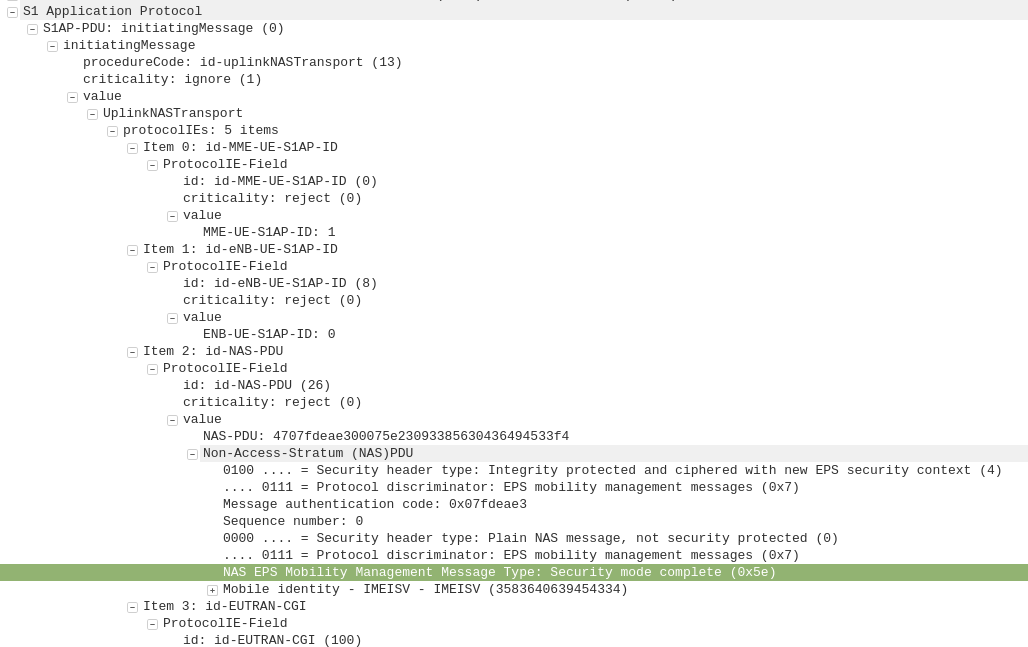
S1AP: UplinkNASTransport, Security mode complete
eNB to MME
After the UE / Subscriber has derived the Ciphering Key (CK) and Integrity Key (IK) from the sent crypto variables earlier, it can put them into place as required by the NAS Security algorithms sent in the Security mode command request.
It indicates this is completed by sending the UplinkNASTransport, Security mode complete.
At this stage the authentication of the subscriber is done, and a default bearer must be established.
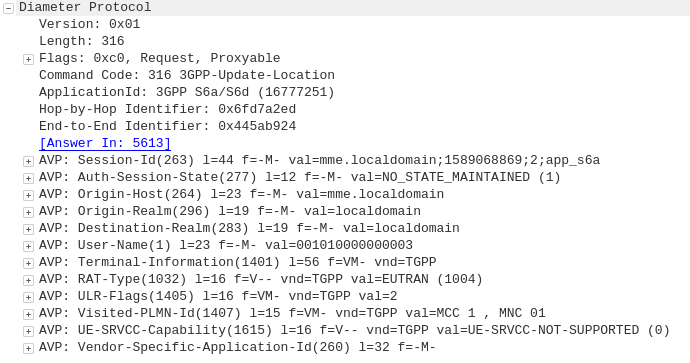
Diameter: Update Location Request
MME to HSS
Once the Security mode has been completed the MME signals to the HSS the Subscriber’s presence on the network and requests their Subscription-Data from the HSS.
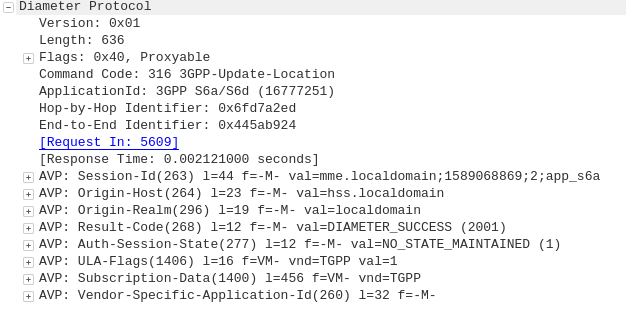
Diameter: Update Location Answer
HSS to MME
The ULA response contains the Subscription Data used to define the data service provided to the subscriber, including the AMBR (Aggregate Maximum Bit Rate), list of valid APNs and TAU Timer.
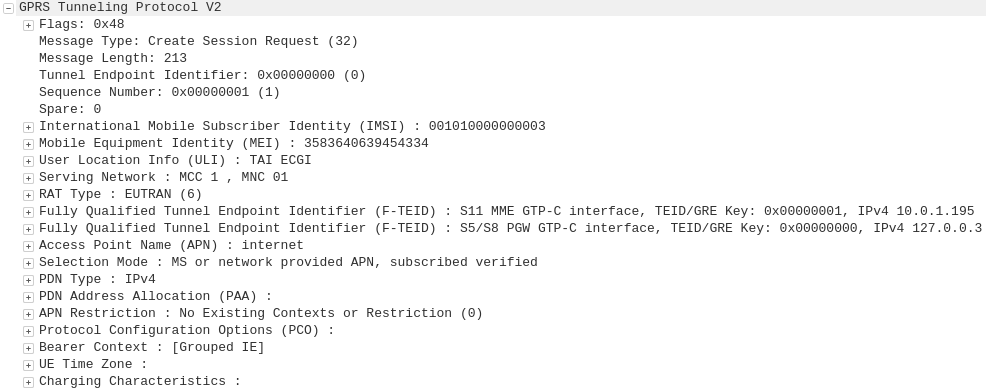
GTP-C: Create Session Request
MME to S-GW
The MME transfers the responsibility of setting up the data bearers to the S-GW in the form of the Create Session Request.
This includes the Tunnel Endpoint Identifier (TEID) to be assigned for this UE’s PDN.
The S-GW looks at the request and forwards it onto a P-GW for IP address assignment and access to the outside world.
GTP-C: Create Session Request
S-GW to P-GW
The S-GW sends a Create Session Request to the P-GW to setup a path to the outside world.
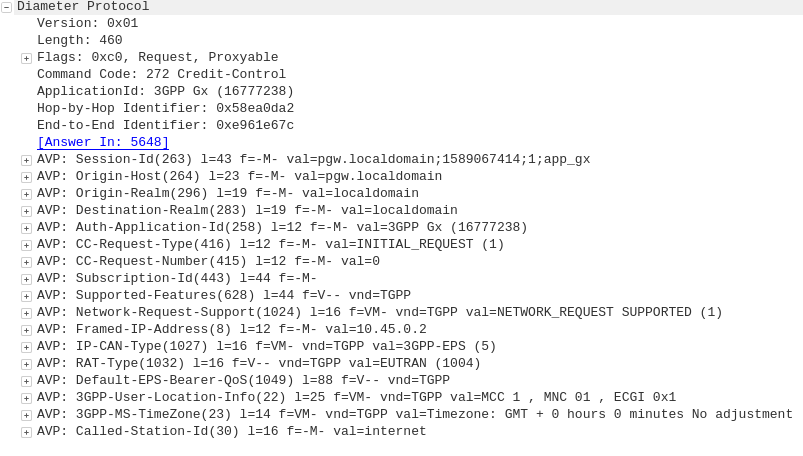
Diameter: Credit Control Request
P-GW to PCRF
To ensure the subscriber is in a state to establish a new PDN connection (not out of credit etc), a Credit Control Request is sent to the HSS.
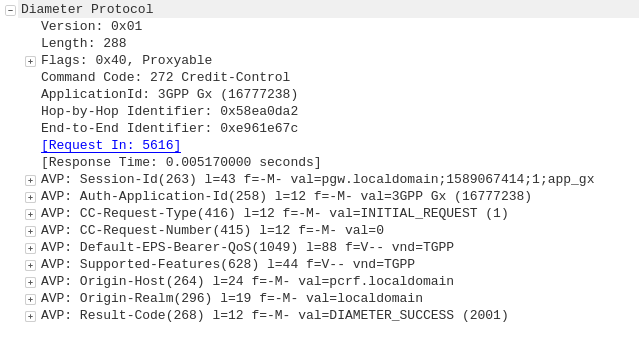
Diameter: Credit Control Answer
PCRF to P-GW
Assuming the Subscriber has adequate credit for this, a Credit Control Answer is sent and the P-GW and continue the PDN setup for the subscriber.
GTP-C: Create Session Response
P-GW to S-GW
The P-GW sends back a Create Session Response, containing the IP address allocated to this PDN (Framed-IP-Address).
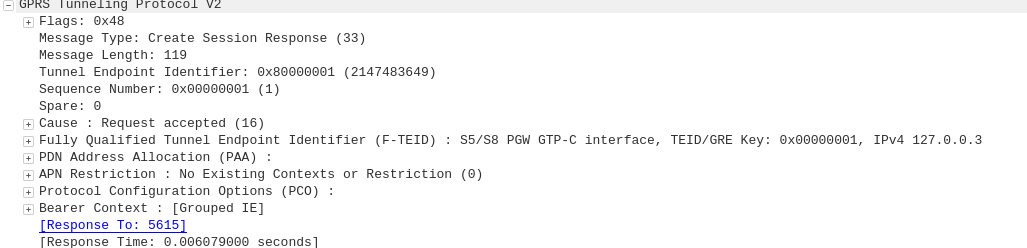
GTP-C: Create Session Response
S-GW to MME
The S-GW slightly changes and then relays the Create Session Response back to the MME,
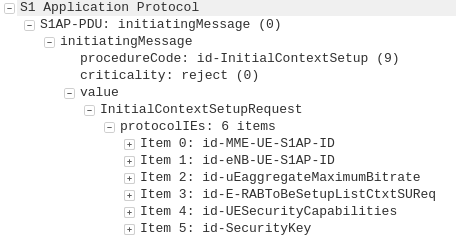
S1AP: InitialContextSetupRequest, Attach accept, Activate default EPS bearer context
MME to eNB
This message is sent to inform the eNB of the details of the PDN connection to be setup, ie AMBR, tracking area list, APN and Protocol Configuration Options,
This contains the Tunnel Endpoint Identifier (TEID) for this PDN to identify the GTP packets.
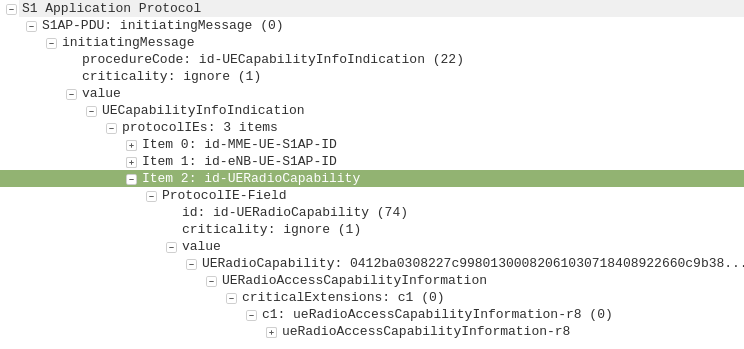
S1AP: UEcapabilityInfoIndication, UEcapabilityIndication
eNB to MME
This message contains the RATs supported by the UE, such as the technology (GERAN/UTRAN) and bands supported on each.
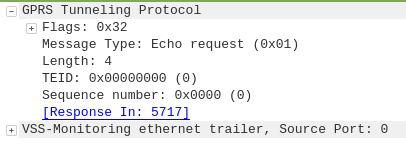
GTP: Echo Request
eNB to MME
To confirm a GTP session is possible the eNB sends a GTP Echo Request to confirm the MME is listening for GTP traffic.
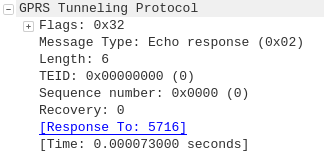
GTP: Echo Response
MME to eNB
The MME sends back a GTP Echo response to confirm it’s listening.
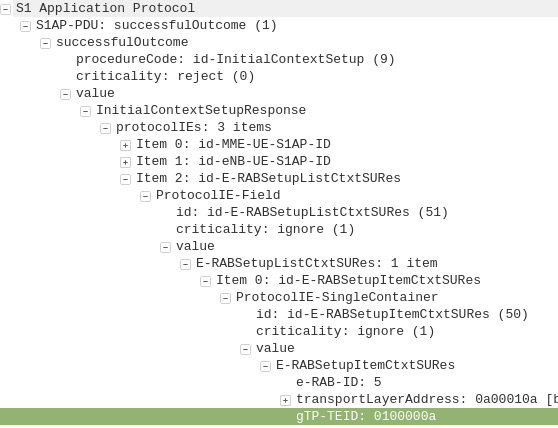
S1AP: InitialContextSetupResponse
eNB to MME
This contains the Tunnel Endpoint Identifier (TEID) and confirmation the context can be setup, but has not yet been activated.
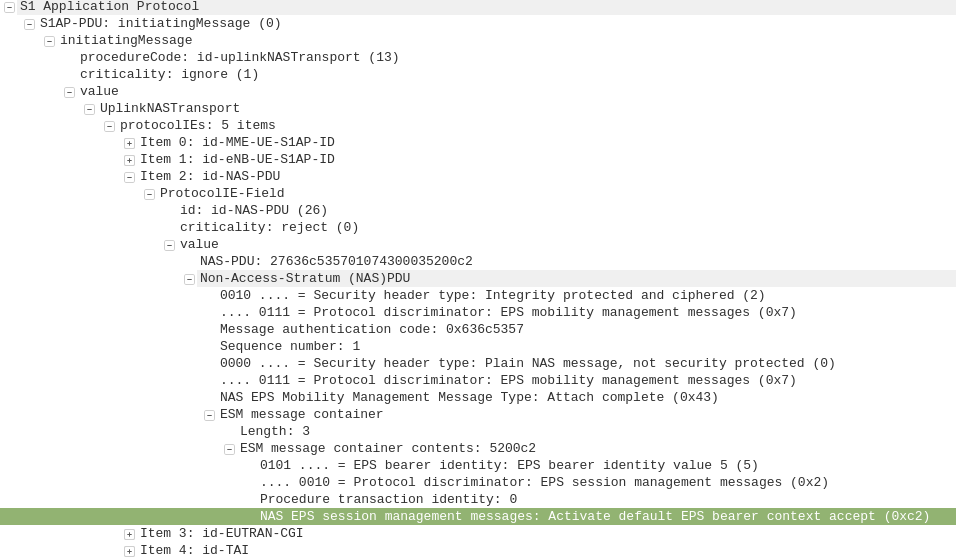
S1AP: UplinkNAStransport, Attach complete, Activate default EPS bearer accept
eNB to MME
This tells the MME the EPS Bearer / PDN session has been activated.
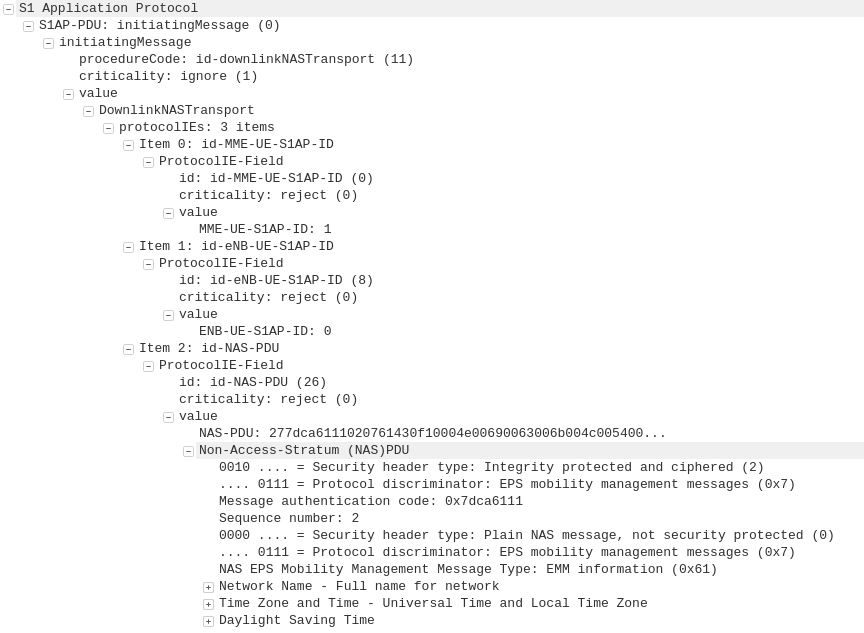
S1AP: DownlinkNAStransport, EMM Information
MME to eNB
This confirms the MME is aware the EPS bearer / PDN session has been activated and provides network name and time settings to be displayed.
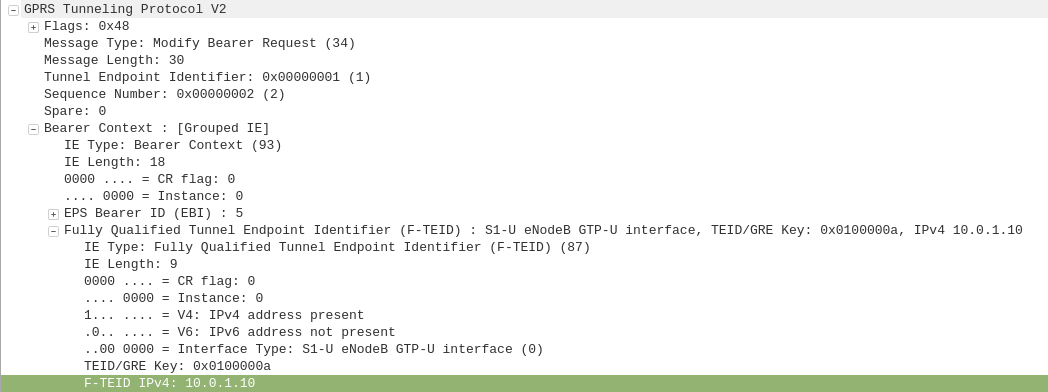
GTP-C: Modify Bearer Request
MME to S-GW
As the MME initially requested the S-GW setup the GTP session / PDN context, the S-GW set it up sending traffic to the MME,
Now the UE is online the GTP session must be modified to move the GTP traffic from the MME’s IP address to the IP Address of the eNB.
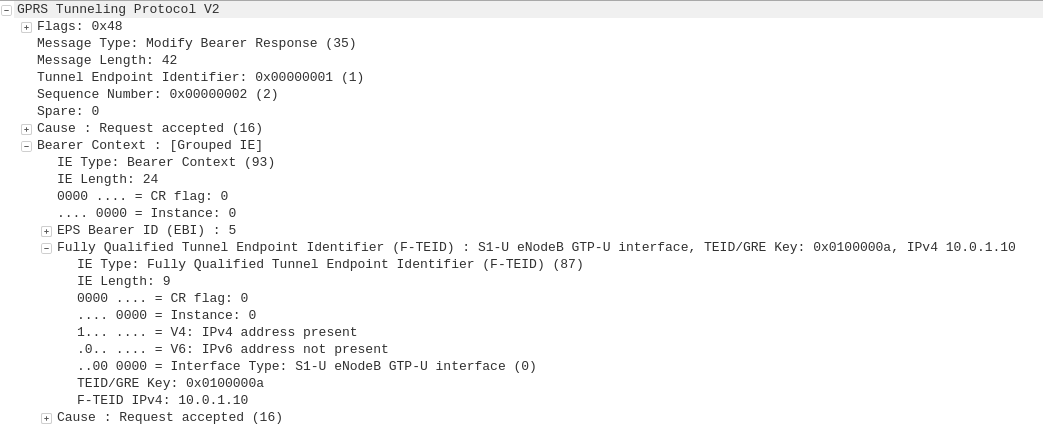
GTP-C: Modify Bearer Response
S-GW to the MME
The S-GW redirects GTP traffic from the MME IP to the IP Address of the eNB.
Nick, just found your website and I’m astonished at your knowledge. How do you build a firm foundation of LTE architecture and understanding call flows with Wireshark? Any good resources/books/videos? I’ve been working as a Tier 3 engineer for a telecom provider and I’m learning everything on the fly but was hoping I could build a good knowledge base that you could point me to.
Nick, I have stumbled on this by chance while trying to have a roaming partner investigate an issue with setting up the default bearer. It is being rejected by the SGW due to the charging characteristics being all set to zero (0). In the ULA from the HSS there is a charging characteristic value for each APN.
When I test it on my own network I see that the charging characteristics are all set to zero (0) however our SGW just sends the CSR towards the customers PGW.
Are you familiar with such an issue and are you able to shed some light on it?
Regards Andi
How P-GW selects the PCRF? If there are two PCRF , Which PCRF will be choosen?
Hi, Where do I have to connect to capture MME-SGW GTP with wireshark
Between the MME and the SGW?
But that’s only GTP-C, GTP-U flows from the eNB to the SGW, not via the MME…
Hi, Nick. Your articles make LTE technology much easier to understand.
I recently encountered an issue where a handset connected to the Internet via Ethernet-over-USB could not extend its IP address lease due to Knox firewall on the handset blocking the DHCP traffic. Understand that the firewall rules will only kick in after the handset has gotten its initial IP assignment.
However, I have no issue when the handsets is connected via LTE. This led me to query how IP address is assigned by the PGW to the UE, and why the Knox Firewall isn’t blocking it. May I seek your views on this?
Thank you.